API Gateway Security: Guarding the Gates of Your Microservices Empire
Posted by: Deepak | May 18, 2024

Categories: API Gateway Security, Microservices Protection, Authentication Methods
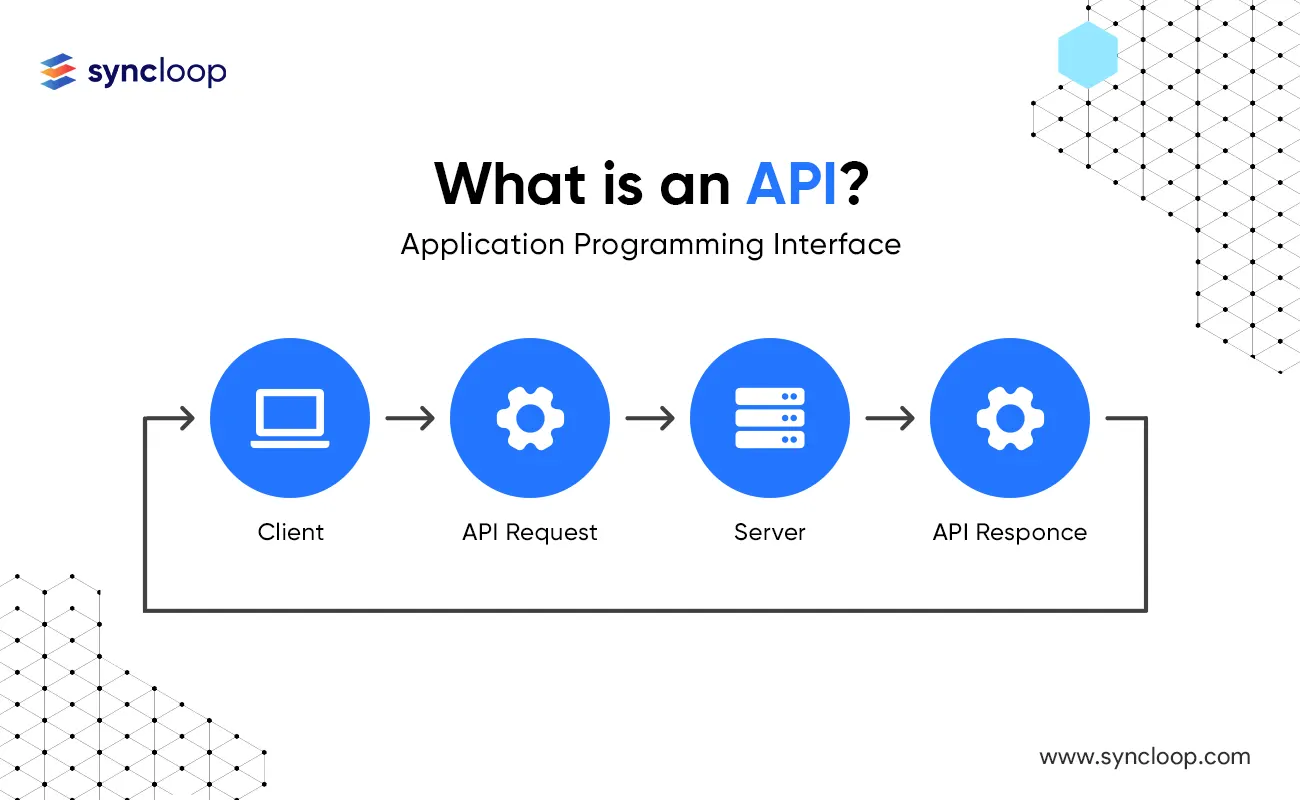
In today's API-driven world, APIs (Application Programming Interfaces) act as the critical gateways to your organization's valuable data and functionalities. Effective API security is paramount for protecting these assets from unauthorized access, malicious attacks, and data breaches. This blog delves into the core pillars of API Gateway security: authentication, authorization, and validation. We'll explore their roles, implementation strategies, and best practices to ensure robust API security.
Why API Gateway Security Matters?
Statistics highlight the growing concern for API security. A 2023 report by Imperva reveals that 74% of organizations have experienced an API security incident in the past year. API gateways, acting as the single point of entry for API requests, become a prime target for attackers. Implementing robust security measures at this level is crucial for mitigating risks and ensuring API integrity.
Here's why API Gateway security is critical:
- Protecting Sensitive Data: APIs often expose sensitive data like customer information, financial records, and internal systems. Strong security prevents unauthorized access and data breaches.
- Enforcing Access Control: API gateways allow you to define who can access your APIs and what actions they can perform, safeguarding your resources.
- Preventing Malicious Attacks: Robust security measures can help prevent DDoS (Distributed Denial-of-Service) attacks, API hijacking attempts, and other malicious activities targeting your APIs.
The Security Trio: Authentication, Authorization, and Validation
Effective API Gateway security relies on a three-pronged approach:
- Authentication: Verifies the identity of the user or application making an API request. Common authentication methods include API keys, OAuth, and OpenID Connect.
- Authorization: Determines what level of access a user or application has to specific API resources and functionalities. This ensures users can only perform authorized actions.
- Validation: Ensures that incoming API requests are formatted correctly, contain valid data, and comply with defined business rules. This helps prevent invalid or malicious requests from processing.
API Gateway Security Implementation Strategies
Here are some key strategies for implementing robust API Gateway security:
- Leverage API Gateway Features: Most API gateways offer built-in security features like user management, token management, and access control policies. Utilize these features to streamline security configuration.
- Implement Authentication Mechanisms: Choose an appropriate authentication method based on your API's needs. API keys are suitable for simple scenarios, while OAuth and OpenID Connect offer more granular access control.
- Enforce Authorization Policies: Define clear authorization policies to restrict access to specific API resources and functionalities based on user roles, permissions, and other criteria.
- Validate API Requests: Implement robust input validation to ensure incoming requests are formatted correctly, contain valid data types, and adhere to defined business rules.
- Utilize Security Tools: Integrate security tools like firewalls, intrusion detection systems (IDS), and API security platforms to monitor API activity, detect suspicious behavior, and prevent attacks.
- Maintain Security Best Practices: Regularly update API gateway software, follow secure coding practices, and conduct security audits to identify and address potential vulnerabilities.
Benefits and Use Cases Across Industries
Implementing robust API Gateway security offers numerous benefits across industries:
- Enhanced Security Posture: Strong API security reduces the risk of data breaches, unauthorized access, and malicious attacks, safeguarding your critical data and applications.
- Improved User Experience: Clear authorization policies ensure users have the necessary access to perform their tasks, leading to a smoother and more secure user experience.
- Compliance with Regulations: Many industries have regulations regarding data privacy and security. Robust API security helps ensure compliance with these regulations.
Here are some industry-specific use cases for API Gateway security:
- FinTech: Financial institutions leverage APIs to offer online banking and mobile payment services. Secure API Gateways ensure user authentication, protect sensitive financial data, and comply with regulations like PCI DSS.
- E-commerce: E-commerce platforms utilize APIs for product information exchange, payment processing, and order fulfillment. Robust API security protects customer data, prevents fraudulent transactions, and safeguards revenue streams.
- Healthcare: Healthcare providers use APIs to share patient data securely between hospitals, clinics, and pharmacies. Secure API Gateways ensure patient data privacy, comply with HIPAA regulations, and protect against unauthorized access.
Latest Tools and Technologies for API Gateway Security
The API security landscape offers a wealth of tools and technologies to enhance your API Gateway defenses:
- API Security Platforms: Platforms like Syncloop, Apigee Security, Kong Guard, and F5 Advanced WAF provide comprehensive solutions for API security, including threat protection, API lifecycle management, and vulnerability scanning.
- Cloud-Based Security Solutions: Cloud providers offer integrated security services for API Gateways, including firewalls, intrusion detection systems, and DDoS protection.
- API Threat Detection and Mitigation Tools: Tools like Threat Stack and Signal Sciences specialize in monitoring API activity, detecting suspicious behavior, and automatically mitigating threats.
Challenges and Considerations for API Gateway Security
While API Gateway security offers significant benefits, there are also some challenges to consider:
- Complexity of Security Configuration: Managing authentication mechanisms, authorization policies, and access control rules across multiple APIs can become complex.
- Keeping Up with Evolving Threats: The cyber threat landscape constantly evolves. Staying updated on the latest attack vectors and implementing appropriate security measures is an ongoing process.
- Balancing Security with User Experience: Overly stringent security measures can hinder the user experience. Striking the right balance between security and ease of access is crucial.
Conclusion
API Gateway security is a critical aspect of protecting your APIs and the valuable data and functionalities they expose. By understanding the core principles of authentication, authorization, and validation, implementing robust security measures, and leveraging the latest tools and technologies, you can effectively safeguard your API ecosystem. Remember, API security is an ongoing process that requires continuous vigilance and adaptation. By adopting a comprehensive approach, you can ensure your APIs remain secure, reliable, and a valuable asset for your organization. As APIs continue to play an increasingly central role in modern applications, prioritizing their security will be key to building trust with users and maintaining a competitive edge in the digital landscape.
Back to Blogs