Implementing OAuth2 and OpenID Connect for Secure API Authentication
Posted by: Deepak | April 12, 2024
Categories: OAuth2, OpenID Connect, API Security
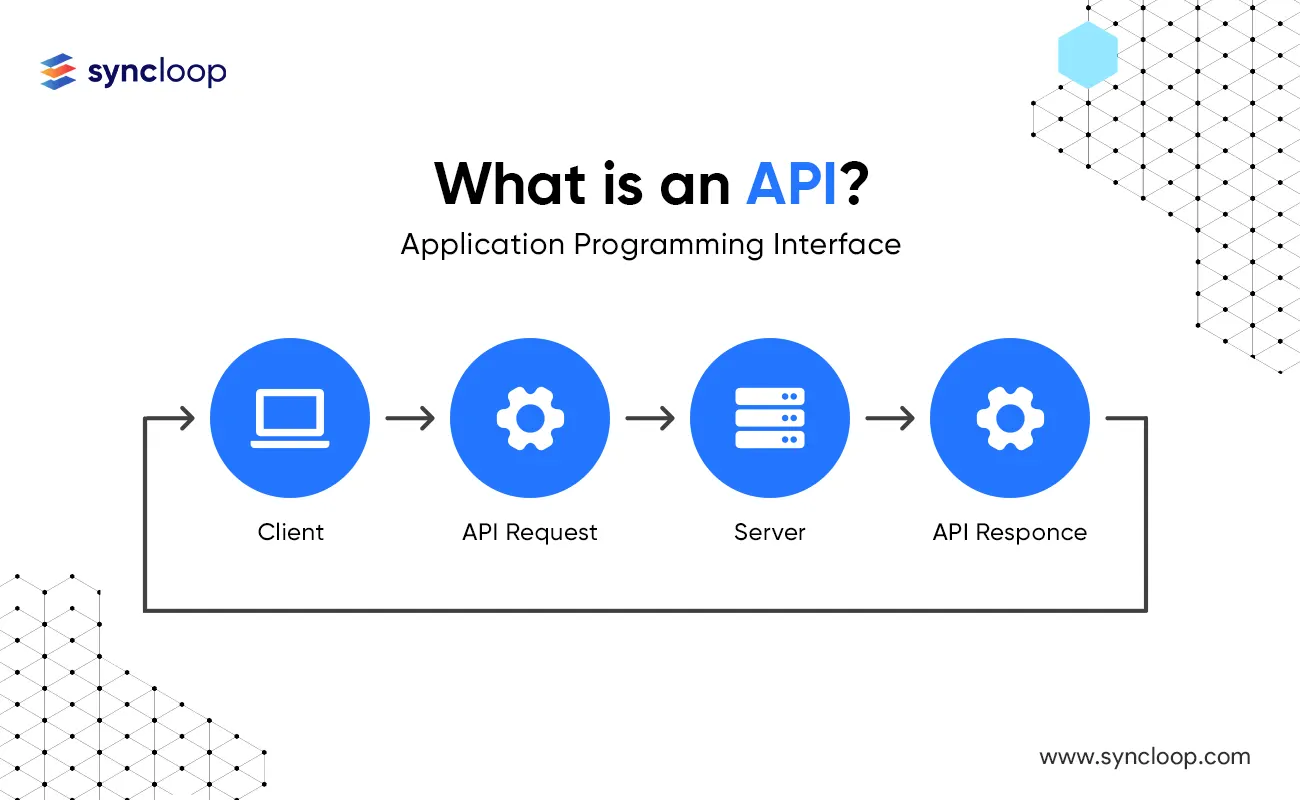
In today's interconnected world, APIs have become the backbone of modern applications. However, securing access to these APIs is paramount. Traditional username/password authentication methods pose security risks and limitations. This is where OAuth2 and OpenID Connect (OIDC) come into play.
This blog delves into OAuth2 and OIDC, explaining their roles in API authentication, exploring the technical details, integration processes, and benefits. Additionally, we'll discuss use cases across various industries and address potential drawbacks.
Understanding OAuth2 and OpenID Connect
OAuth2: An authorization framework that enables secure delegation of user access to protected resources on an application's behalf. It focuses on granting access tokens for specific resources without revealing user credentials.
OpenID Connect (OIDC): An identity layer built on top of OAuth2 that simplifies user authentication. It allows applications to obtain user information (like name, email) from an authorization server, streamlining user login experiences.
Here's a breakdown of the key actors involved:
- Resource Server: The API that holds the protected resources and validates access tokens.
- Authorization Server: The server responsible for issuing access tokens based on user credentials or authorization grants.
- Client Application: The application requesting access to the protected resources on the resource server.
- Resource Owner: The end-user who grants access to their data.
Statistics showcase the widespread adoption of OAuth2 and OIDC. A 2023 study by Okta revealed that 80% of developers use OAuth2 for authorization, highlighting its critical role in modern API security.
Benefits of Using OAuth2 and OIDC
Implementing OAuth2 and OIDC offers several advantages over traditional authentication methods:
- Improved Security: Eliminates the need for storing user credentials within the client application, reducing the risk of data breaches.
- Delegated Authorization: Enables users to grant access to specific resources within an API, offering granular control over data sharing.
- Simplified User Experience: OIDC streamlines user login by leveraging existing login sessions from trusted providers like Google or Facebook.
- Scalability and Flexibility: Supports various client types (web, mobile, native apps) and integrates seamlessly with different identity providers.
The OAuth2 Flow: A Step-by-Step Guide
The OAuth2 authorization flow involves several steps:
- Authorization Request: The client application redirects the user to the authorization server's login page.
- User Authentication: The user enters their credentials and authorizes the client application to access their data.
- Authorization Grant: If successful, the authorization server issues an authorization code and redirects the user back to the client application.
- Access Token Request: The client application sends the authorization code back to the authorization server along with its client credentials, requesting an access token.
- Access Token Response: The authorization server verifies the request and issues an access token specific to the requested resource.
- API Access: The client application utilizes the access token to access the protected resources on the resource server.
Integration Process: Implementing OAuth2 and OIDC
Integrating OAuth2 and OIDC involves several key steps:
- Choose an Authorization Server: Select a trusted authorization server like Auth0, Okta, or Azure Active Directory.
- Register Your Application: Register your client application with the chosen authorization server, providing details like redirect URIs and scopes (requested permissions).
- Configure API Access: Configure your API to validate access tokens issued by the authorization server.
- Implement Client-Side Logic: Develop the client-side logic in your application to handle user redirection, authorization code exchange, and access token utilization.
- Error Handling and Security: Implement robust error handling mechanisms to address potential authorization failures and ensure secure storage and usage of access tokens.
Latest Tools and Technologies
The OAuth2 and OIDC ecosystem is constantly evolving. Here are some of the latest tools and technologies that can aid your implementation:
- OpenID Connect Libraries: Libraries like OIDC-Client (JavaScript) and Nimbus (Java) simplify client-side integration with OIDC providers.
- API Gateway Integration: API gateways like Syncloop, Apigee and Kong offer built-in support for OAuth2 and OIDC, enabling easy integration for secure API access.
- Cloud-Based Solutions: Cloud providers like AWS, Azure, and GCP offer managed authentication services with built-in OAuth2 and OIDC capabilities.
Use Cases and Real-World Applications
OAuth2 and OIDC find application across various industries to securely authenticate users and access APIs:
- Social Media: Platforms like Facebook and Twitter allow applications to login users and access profile information using OAuth2 and OIDC.
- E-commerce: Online stores can utilize OAuth2 and OIDC to allow users to sign in with existing accounts (like Google or Facebook) and access purchase history or address information from those providers.
- FinTech: Financial institutions can leverage OAuth2 and OIDC to securely connect with third-party applications for financial data aggregation or payment processing, while maintaining user control over data access.
- IoT (Internet of Things): OAuth2 and OIDC can be used to authenticate mobile applications accessing data from connected devices, ensuring authorized access to sensor data and device controls.
Disadvantages and Considerations
While OAuth2 and OIDC offer significant benefits, there are also some considerations to keep in mind:
- Complexity: Implementing OAuth2 and OIDC can involve more complexity compared to traditional authentication methods, especially for beginners.
- Third-Party Dependence: Reliance on a trusted authorization server introduces a dependency on external infrastructure.
- Potential Security Concerns: Improper implementation of OAuth2 and OIDC can still introduce security vulnerabilities, so proper configuration and security best practices are crucial.
Conclusion
OAuth2 and OpenID Connect are powerful tools for securing API access in modern applications. By understanding the core concepts, implementing the authorization flow, and leveraging available tools, you can build robust and secure API authentication mechanisms. Remember, choosing a trusted authorization server, implementing proper error handling, and prioritizing security best practices are essential for a successful OAuth2 and OIDC integration. As the API landscape continues to evolve, OAuth2 and OIDC will remain a cornerstone of secure and user-centric API access control.
Back to Blogs